If you missed our recent webinar on 2024’s U.S. privacy laws or if we simply didn’t have time to get to your question, don’t worry; we kept track of the questions asked at the end of our webinar and wrote down responses from experts at Osano and Husch Blackwell. You can also access the webinar recording here.
Note that we’ve lightly edited the questions and responses for clarity and combined questions on the same subjects. Read on to learn what attendees were most curious about regarding the 2024 U.S. state privacy laws.
1. What Is a Cure Period? What Does It Mean for a Cure Period to Sunset or Not Sunset?
Cure periods are a window of time that a violator is given to fix (or “cure”) their violation. If an organization is found to be in violation of a law with a cure period, the state attorney general or enforcement agency will notify the organization of their violation first and give them 30 to 60 days to cure the violation before they will be penalized. (The exact duration depends on the given law.)
Most, but not all, state privacy laws have a sunsetting cure period. After a certain amount of time has passed, authorities will no longer be obligated to offer a cure period before applying penalties to violators. Some states, however, have a non-sunsetting cure period, meaning authorities will always offer a cure period to violators before applying penalties.
Even if a law has a cure period, however, it can be quite difficult to cure a violation in time. The first enforcement action under the CCPA, for example, was against Sephora; they were given a cure period but did not fix the violations in time.
2. What Is the Definition of a "Known Child"?
Many state privacy laws treat the data of a “known child” as being more sensitive than other data. Thus, it requires additional protection, and associated violations come with higher penalties.
The definition of a “known child” varies from law to law, but typically refers to users under the age of 13, 16, or 18. Some states also have child-specific data privacy laws, like the California Age-Appropriate Design Code Act as well.
As for whether or not the child is “known,” most state privacy laws don’t expect businesses to read their users'c minds—children can easily access many products and services without the business’s knowledge. However, if that product or service is explicitly marketed toward children, if the business collects demographic information that reveals a user's age, or if the business is otherwise aware or suspects that user is a child, then the user might qualify as a known child.
3. Did This Webinar Provide CLE Credit?
We do not have a CLE code available for this webinar but, depending on your jurisdiction, you may be able to use this for self-study. Going forward, we are planning to offer CLE for sessions with law firms, and we'll mark this on the event information.
4. Where Can I Find DPIA Templates?
There are a few places to access data protection impact assessment (DPIA) templates. The UK Information Commissioner's Office has a template, the IAPP offers a template, and the Osano Platform provides templates and assessments in the app.
5. If DPIAs Are Required When There’s a Risk of Significant Harm to an Individual's Rights and Freedoms, How Do You Evaluate That Risk Without First Completing a DPIA?
First, you can look at the circumstances where a DPIA is explicitly required, like profiling, targeting advertising, sales of data, and so on. Is this processing similar to that? Does it involve sensitive data? Does it involve children’s data?
To a certain extent, you need to go with your gut on whether or not a DPIA is required. Does it seem like something a consumer could have a concern with? If so, executing a DPIA is probably a safe bet. When in doubt, lean towards conducting a DPIA. If processing activities seem similar to any of the circumstances where a DPIA is explicitly required, then definitely consider conducting one.
6. How Do These Laws Impact B2B Businesses Versus B2C Businesses?
Commercial information is often exempt in data privacy laws, which generally consists of employee data. (The CPRA is a notable exception and does apply to employee data.) However, if you collect a consumer’s personal data—even if that consumer is the employee of another business—then that data processing is still regulated.
You may also receive personal data from another business for whom you are a vendor. Most data privacy laws require you to treat that data with the same level of protection as the business that originally collected it.
7. Do Data Privacy Requirements Apply Based on the Consumer’s Residence or Where the Company Is Based?
They are based on the consumer's state of residence. For instance, a company based in California would fall subject to California’s law (the CPRA) if it processes the personal information of 100k or more California residents. If the California-based company is processing the personal data of 100k or more Oregon residents, it would also be subject to Oregon’s new law.
8. How Do You Record Consent for Sensitive Data Processing? Is It the Same as Using a Consent Management Platform?
Some CMPs do offer capabilities for securing consent at touchpoints that collect sensitive data. U.S. data privacy laws generally require consumers to opt in prior to the collection of sensitive data, and they punish violations associated with sensitive data more harshly. Because of that, many businesses seek to not collect sensitive data in the first place or even use a manual process, like signing a form, to ensure they collect consent appropriately.
9. What Is a DSAR?
DSARs, or data subject access requests, refer to the spectrum of requests that consumers are permitted to make under data privacy regulations. Businesses usually have 45 days to respond to a DSAR or else they will be in violation of the law.
Different laws provide different rights, but they often include:
- The right to be informed about the collection and use of personal data.
- The right to access personal data and how it's processed. This is the most common sort of DSAR, and it’s why DSARs are referred to as access requests.
- The right to rectify inaccurate or incomplete personal data.
- The right to request the deletion of personal data.
- The right to data portability. Data subjects must be allowed to take their data from one platform to another and do so easily, safely, and securely.
- The right to object to automated decision-making and profiling. Data subjects have the right to say no to solely automated decisions—including profiling—being made about their data that could have a legal or similarly significant effect on them.
DSARs are also often referred to as subject rights requests, or SRRs.
10. What Law Has the Highest Standards?
California is often perceived as the strictest U.S. privacy law because its requirements are so prescriptive and because it has an active agency enforcing the law. However, California’s model doesn’t perfectly align with other state laws. For example, Colorado is seen as having stricter requirements around consent.
The GDPR is generally considered stricter than most other data privacy laws, but again, it’s something of an apples-and-oranges comparison—you would still need to adjust to be compliant with an individual data privacy law. Pursuing compliance with the CPRA and/or the GDPR is likely to get your organization closer to compliance with other state privacy laws, however.
11. Are Businesses Penalized for Each Violation Per Consumer?
Yes, though it’s important to keep in mind that you can commit multiple violations against an individual consumer. For example, it’s possible that you failed to respect a consumer's consent choices and failed to respond to their subject rights requests. If you did that 1,000 times, then you would have committed 2,000 violations.
12. Privacy Protection Usually Sits With the Legal Side of an Organization. With New Emerging Technologies, How Should Teams Be Structured to Include Both Legal and Technical Expertise?
There is a lot of overlap between the legal requirements, compliance requirements, and actual compliance operationalization. Regardless of what your company is doing, it's just important to get the people that are interested and can help drive compliance forward. We’ve seen companies that have champions or stakeholder groups that share feedback with one another to make sure data privacy has been successfully operationalized at their organization.
Once you get through the data mapping and data inventory process, you’ll know where personal data is being processed across your organization. Anybody who handles that data, such as the marketing, product development, and information security teams, should be involved in your privacy program to one degree or another.
13. Which Upcoming State Laws Require a Consent Management Platform? Is the CPRA’s “Limit the Use of My Personal Information” Link Not Sufficient?
Technically, none of the state laws legally require a consent management platform—but using one will be a big help. Generally, consent management platforms (CMPs) can keep you in compliance with all of the U.S. privacy laws and internationally by presenting a compliant cookie banner for the given jurisdiction.
14. What If Your Data Governance Is All Over the Place and You Don't Know What Data Is Where? How Do You Even Start to Comply?
Start with data inventory and mapping. In order to handle data compliantly, you have to figure out where the data is, who it’s being shared with, what departments are using it, and so on.
You can’t begin to tackle consumer requests, provide security, get vendor agreements in place, provide accurate notice, or even properly manage consent unless you know where the data is and what’s being done to it. Data mapping tools can help you take this important first step.
15. Tracking Down Cookie Details Is a Major Pain. Would You Expect State, Federal, Or EU Legislation to Ever Address This with Some Sort of Global Registry?
That certainly would be helpful! While there is no official government registry of cookies, there are crowd-sourced databases that can be accessed to identify cookies. The associated vendor will also often list out the cookies they use on their website or in their documentation. And, if you use Osano’s cookie consent solution, we provide classification recommendations that can help you treat each cookie in a compliant manner.
16. For Businesses That Are Subject To laws like the GLBA and HIPAA, Most New Privacy Laws Provide Entity-Level Exemptions. Some, However, Only Provide for a Data-level Exemption Under These Other Laws. Do You Expect Future Laws to Lean Towards the Entity-Level Exemption or the Data-Level Exemption?
For the unfamiliar, an entity-level exemption means that if an organization is subject to the GLBA (or HIPAA or any other law that would make them exempt), then all of their processing activities are exempt from the data privacy law. A data-level exemption means that only the processing activities associated with the relevant data are exempt, and the rest of their data processing activities must be compliant.
There has been a mixed bag with whether state privacy laws apply data-level or entity-level exemptions. We expect that to continue without any tendency one way or another.
17. How Do You Account for Washington My Health My Data Law and the Impact on Privacy Since the Law Considers All Patients "Consumers"?
The Washington My Health, My Data Act (MHMDA) defines consumers as Washington residents or persons whose consumer health data is collected in Washington. This definition could include non-residents providing their health data to Washington-based businesses. Simply put, most Washington-based businesses that collect health data will need to comply with the MHMDA, and most businesses that collect health data from Washington residents (whether or not they are based in Washington) must comply with the MHMDA.
18. What Are You Expecting in 2024 as Far as More States Passing Privacy Legislation?
We anticipate a continuation of the trend that we have been seeing—more and more states passing comprehensive consumer privacy laws modeled after the Virginia and Colorado laws, such as the Washington Privacy Act.
As of this writing, New Hampshire and Wisconsin both have privacy bills that are fairly far along in the legislative process, and nearly every other state has had some sort of data privacy bill introduced. There is also the possibility that a federal data privacy bill gets passed, potentially superseding these laws.
19. Can You Clarify About the Washington Privacy Model? Has Washington Adopted a Privacy Law Finally or Have They Proposed One?
The Washington Privacy Act has been proposed multiple times and has never made it across the finish line. However, many state legislators followed that model for their own state privacy laws. It may be passed in 2024, but that remains to be seen.
20. Can You Elaborate on the "Data Mapping" Exercise? How Complex Is It? Is a Manual Approach Sufficient?
It depends. Some organizations with smaller operations do manual data maps, which they accomplish by sending around questionnaires and Excel sheets that department heads have to fill in with information on what personal data they collect, what they share, and so on.
Then, there are really large companies that hire vendors who specifically conduct data mapping and data inventory exercises. These vendors go into every office, and they conduct interviews with all of the heads of departments and create a more sophisticated data map.
In both cases, the process can be pretty lengthy, taking months at a time.
A better approach for most companies, however, is to use a data mapping tool, which strikes a balance between accuracy, spend, and timeliness—data mapping is a foundational compliance exercise, after all, so it’s important to complete early on.
22. Don’t All of the Privacy Laws Apply to Employee Info Too and Not Just Customer Data?
Most state consumer privacy laws exempt employee data; at this time, the CCPA (as amended by the CPRA) is the only state privacy law that applies to employee data.
Stay Up to Date on Osano Webinars, Events, and Privacy News
Want to make sure you’re the best-informed person in the room when it comes to data privacy?
Sign up for the Osano newsletter, Privacy Insider!
We’ll send you a curated list of the week’s biggest data privacy stories, new assets and resources from Osano, and information on special events, like webinars, conferences, and more.
U.S. Privacy Laws Checklist
Need to get compliant with 2024's state data privacy laws? This checklist will show you what to do and when.
Download Your Copy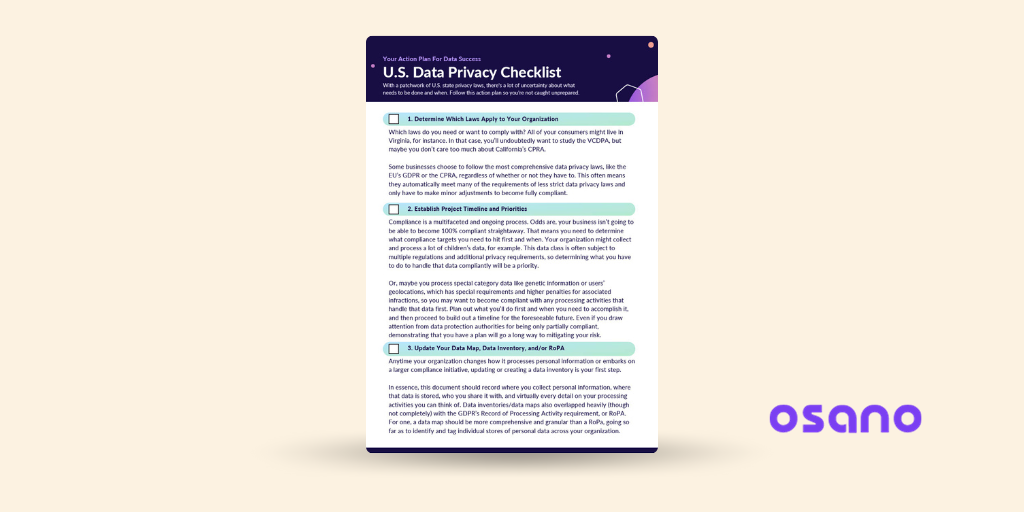
Osano Staff
Osano Staff
Osano Staff is pseudonym used by team members when authorship may not be relevant. Osanians are a diverse team of free thinkers who enjoy working as part of a distributed team with the common goal of working to make a more transparent internet.
.webp?width=1220&height=1090&name=Osano-guarantee-seal%20(1).webp)