In today’s digital environment, businesses seem to have vendors for everything. How you run your meetings, how you talk to customers, how you communicate internally—practically every aspect of a modern business is supported by third-party vendor. That’s why vendor risk management and third-party risk management (TPRM) is so essential. Research shows that organizations share their data with over 730 different vendors. And often, those vendors share your data with their own vendors.
Okay, vendor risk management is important: what exactly is it, and how can you implement it?
We’re glad you asked.
What’s the difference between vendor risk management and third-party risk management?
Often used interchangeably, vendor risk management and third-party risk management (TPRM) are both terms used to describe continuous monitoring and risk mitigation associated with outside people and organizations with which your company does business.
In short: vendors are a subset of third parties. While this may sound confusing, it really boils down to subtle differences.
- Vendor: A vendor supplies a product or service to your company or organization. This could include your software as a service (SaaS) provider, your company’s website hosting service, or an office equipment supplier.
- Third Party: A third party is an individual or company that facilitates a transaction but is not a primary party, such as a business partner, consultant, or even your customers. It gets a little tricky because “third party” has become an umbrella term that includes vendors, suppliers, providers, partners, contractors, and consultants. All vendors are third parties, but not the other way around.
What is vendor risk management?
Outsourcing aspects of your operations to vendors is a necessity in modern business. Vendor risk management is understanding who your vendors are, their privacy practices, and the risks associated with doing business with them. If a breach did occur through one of your vendors, what impact would it have on your business, its operations, and its customers?
There are many types of risks, and your company’s threshold for each type may vary depending on the vendor and its access to your company’s data. For example, a company that handles your organization’s social media is not as big of a risk as a vendor that processes payroll simply because of the types of information they each need to provide service. Some types of risk include:
- Cybersecurity risk: Security breaches can disrupt your business’s information technology systems and leave you open to data loss.
- Legal risk: If your vendors aren’t following applicable regulations, your company could be held liable, particularly in highly regulated markets like financial services, healthcare, and government organizations.
- Privacy risk: While privacy risk overlaps with legal risk, it’s not a one-to-one match. Your vendors might violate data privacy regulations and put you at legal risk, but they might also fail to meet your internal standards for consumer privacy. That could damage your brand and operations.
- Reputational risk: When a company suffers a security incident, either directly or through a vendor, its reputation takes a hit. Poor public perception could lead to reduced revenue, loss of customers, and more.
- Financial risk: A vendor could put your company in financial peril by causing issues with the supply chain, overspending, or by impacting revenue-generating activities.
- Operational risk: Depending on how critical the vendor is to your company, a vendor’s ability to complete services as promised could have a direct impact on your organization’s operations.
The link between data privacy violations and vendor risk
Without a robust third-party vendor risk management process, a company opens itself up to a host of consequences ranging from regulatory actions to the potential shuttering of the business. In fact, 60% of small businesses that suffer a cyberattack are unable to withstand the impact and end up going out of business within six months, according to the National Cyber Security Alliance.
That’s because of the costs associated with recovery and remediation, reputational damage, or paying cyberattackers’ ransoms. But a major cost associated with data breaches are fines related to the data privacy violations uncovered by a breach.
Today, data privacy is more important than ever. The European Union’s GDPR ushered in a new era of data privacy. Now if businesses want to operate in a given region, they have to comply with the patchwork of U.S. privacy laws, like California’s CPRA, and other international laws, like the Brazilian LGPD or Canada’s PIPEDA.
Because vendor risk is such an real threat to data privacy, many of these consumer data protection laws have requirements for what data can be transferred to vendors and what vendors are allowed to do with that data.
When vendors fail to live up to these standards, they increase their (and your) risk for a data breach; when such a breach occurs, it’s often because of negligence in their duty to protect your customers’ data.
Why is vendor risk management important?
Managing and reducing risks—particularly with regard to security and privacy—should be a priority for all companies. Vendors often have access to a lot of your company’s (and, more importantly, your customers’) information.
If a vendor doesn’t follow cybersecurity best practices, their vulnerabilities become your vulnerabilities. The average cost of a data breach in the United States in 2022 was $9.4M ($4.3M global average), according to a report released by IBM. Legal and investigative costs, lost revenue and investment, and negative impacts to a company’s reputation are all other potential costs of a data breach.
Many companies have become targets of cyberattacks. In one recent example, Texas-based SolarWind’s software was hacked without immediate detection. When software updates were sent to their 33,000 customers, the malicious code went with it creating a “backdoor to customer’s information technology systems, which hackers then used to install even more malware that helped them spy on companies and organizations,” Business Insider explained.
This highlights the importance of vendor risk monitoring and management—had more companies identified SolarWinds’s vulnerabilities earlier, they might have gone with another vendor.
How to manage vendor risk
Vendor risk management is an ongoing process that, when practiced consistently, can help protect your organization from risks introduced by vendors.
- Ensure you understand your company’s current vendor landscape. Conduct an audit to gain an understanding of who your vendors are, what access they have to data and information, and what risks they could pose to your company. Creating a vendor inventory can highlight redundant vendors, vendors who are no longer used but who may still have access, and high-risk vendors.
- Classify vendors by risk. Categorize your vendors into tiers based on their risk and how critical they are to the company.
- Create an effective assessment process. Make sure you understand who is in charge of each task, from selection to due diligence, onboarding vendors, assessment questionnaires, and reviewing assessments. Define how often you need to reassess vendors and what the process looks like. If you’re not sure what a vendor assessment looks like, don’t worry: There are standard templates you can use to develop these assessments.
- Choose a control framework and risk methodology. There is not a single control framework that’s right for every organization, but every company should choose the one that best meets their needs, such as NIST or ISO.
- Continuously monitor risk. Continuously is the key word here. Even if a vendor checked all the boxers initially, they could introduce risk later. Every time something changes, a vendor needs to be reevaluated to ensure they’re still in compliance and not introducing your company to undue risk.
If you’re thinking “That sounds complicated,” that’s because it is—when it’s done manually.
Osano can help
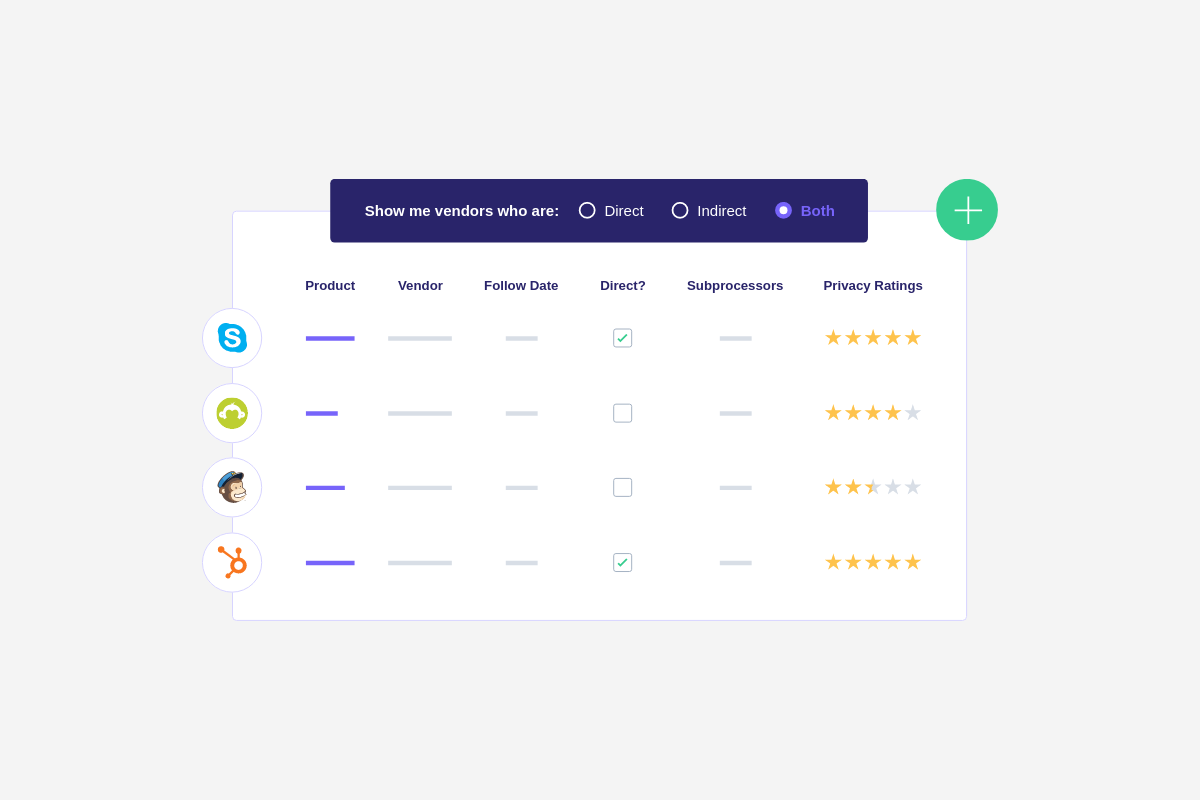
Osano’s Vendor Risk Management solution automates the privacy aspect of vendor risk management by:
- Keeping track of vendors and regulations.
- Providing vendor assessment templates you can rely on when evaluating new or existing vendors.
- Distributing ongoing assessments from a centralized location.
- Quantifying vendor risk in a privacy score, calculated based on machine learning techniques, privacy expert judgments, and a 163-item ontology.
- Tracking and storing compliance information.
- And more.
This creates a scalable, manageable, and sustainable process that will save your company time, money, and headaches related to vendor risk.
Schedule your free demo today to learn how Osano can help continuously monitor and manage your vendor risk.
U.S. Data Privacy Checklist
Stay up to date with U.S. data privacy laws and requirements.
Download Your Copy
Osano Staff
Osano Staff
Osano Staff is pseudonym used by team members when authorship may not be relevant. Osanians are a diverse team of free thinkers who enjoy working as part of a distributed team with the common goal of working to make a more transparent internet.
.webp?width=1220&height=1090&name=Osano-guarantee-seal%20(1).webp)