In the complicated web that is data privacy law, there are a lot of acronyms. There are acronyms for everything from laws and regulations to types of data, roles, frameworks, and more.
Unpacking the meaning of similar concepts—such as personal information (PI) and personally identifiable information (PII)—may seem burdensome, but for businesses tasked with complying with a growing number of regulations, sifting through the nuances is critical to staying compliant.
This blog focuses on PII, its role in the context of data privacy, as well as differences between PII and PI, its relation to various regulations, and how to remain compliant.
What Is PII Data?
As you’ll learn in this blog, different laws define PII differently, but in general, PII is defined as information that can be used to identify a person or trace an individual’s status or activities. These can include data such as:
- Full name
- Email address
- Phone number
- Biometric records
- Social Security number
- Passport information
- Bank account number
- Government-issued ID number
- Medical information
- Educational data
- Financial details
- Employment information
Let’s look at a common, everyday PII data example: applying for a credit card online. For the credit card issuer to assess your creditworthiness, the application requires a host of information, from your full legal name and address to your social security number, employment details, annual income, and other details. These details are prime examples of PII, as they directly identify you and distinguish you from another individual.
PII is collected by organizations in the course of most activities, from visiting the doctor to shopping, for financial transactions, banking, checking into the gym, and so on.
Why Does PII Matter in the Context of Data Privacy?
PII is at the core of data privacy. If PII is lost by an organization, it could cause substantial harm, including identity theft, fraudulent use of the information, or other attacks. Protecting personally identifiable information is critical for preserving Individuals' privacy, retaining their trust, and avoiding painful fines and penalties.
According to the Pew Research Center:
- 26 percent of Americans reported that someone had put fraudulent charges on their debit or credit card in the previous 12 months.
- 11 percent have had their email or social media accounts taken over without permission.
- 7 percent have had someone attempt to open a line of credit or apply for a loan in their name.
While breaches of PII can have significant impacts on consumers, a breach could also have far-reaching impacts on companies—primarily with hefty fines and reputational damage. To date, the largest fine on record was issued by China’s cybersecurity regulator to a Chinese ride-hailing company for $1.2 billion. In the EU, Meta was fined €1.2 billion for improperly transferring data (including PII) out of the EU. And in the U.S., Sephora was fined $1.2 million for selling/sharing its consumers’ PII without informing them or giving them the opportunity to opt out.
PII or PI: What’s the Difference?
By now, you may be thinking, “But wait, you mentioned PI. What’s the difference?”
Commonly confused, personal information, or PI, is “information that identifies, relates to, describes, is capable of being associated with, or could be reasonably linked (directly or indirectly) with a particular person.” If that definition sounds a lot like the definition of PII data, that’s because there is a significant overlap between the two.
The California Privacy Protection Act (CCPA) uses the term “personal information,” to include other data, such as IP addresses; biometric, location, or audio information; and personal device identifiers. Furthermore, personal information could include data that, when combined with other information, could become PII. As an example, the name “John” is personal information, but is only indirectly linked to a specific individual. There are many Johns out there, after all. Combined with an address or a last name, that PI suddenly becomes PII. It’s not just personal information, it’s personally identifiable information—i.e., information that can be used to identify an individual person.
The General Data Protection Regulation (GDPR) and PII
Like most privacy laws, the GDPR has extraterritorial reach—meaning, if your company operates in the United States and stores or processes PII data of European citizens, it must comply with the GDPR.
The GDPR defines personal data as: "any information relating to an identified or identifiable natural person ("data subject"); an identifiable natural person is one who can be identified, directly or indirectly, in particular by reference to an identifier such as a name, an identification number, location data, an online identifier or to one or more factors specific to the physical, physiological, genetic, mental, economic, cultural or social identity of that natural person. Note that this definition of personal data is broader than strictly PII.
If personal data is made anonymous (by removing direct and indirect personal identifiers) and cannot be used to identify an individual, it’s no longer considered “personal” under the GDPR. However, even if data has been encrypted and de-identified, if it could later be used to re-identify a person, it is still considered personal data.
GDPR also references “pseudonymization,” or processing personal data in a way in which the data can no longer be attributed to a specific data subject without the use of additional information. Because pseudonymization can eventually be linked back to an individual with the addition of further information, it is considered personal data under the GDPR.
PII Data and the California Privacy Rights Act (CPRA)
Mirroring the GDPR in many aspects, the California Consumer Privacy Act (as amended by the CPRA) is the most stringent US data privacy law. The CPRA defines personal information as information that “identifies, relates to, describes, is reasonably capable of being associated with, or could reasonably be linked, directly or indirectly, with a particular consumer or household.” Adding “household” to its definition is unique to California. Again, this definition of personal information is broader than PII.
Some examples of personal information under the CPRA include:
- Real name, alias, postal address, unique personal identifier, online identifier, internet protocol address, email address, account name, Social Security number, driver’s license number, passport number, or similar identifiers;
- Commercial information, including records of personal property, products or services purchased, obtained, or considered, or other purchasing or consuming histories or tendencies;
- Biometric information;
- Internet or electronic network activity information;
- Geolocation data;
- Audio, electronic, visual, thermal, olfactory, or similar information;
- Professional or employment-related information;
- Inferences used to create a profile about a consumer reflecting their preferences, characteristics, psychological trends, predispositions, behavior, attitudes, intelligence, abilities, and aptitudes;
- Sensitive personal information (SPI).
Publicly available information or lawfully obtained, truthful information that is a matter of public concern and deidentified or aggregate consumer information is not considered personal information.
SPI is a subset of personal information that reveals what the law considers more likely to cause harm if it’s misused, which is why CPRA gives consumers the right to limit the use of their sensitive personal information.
How to Comply With PII Data Privacy Requirements
To comply with PII data privacy requirements, organizations that collect personal data about consumers must understand the information they collect; applicable regulations, such as the CCPA, CPRA, GDPR, and others; and how each impacts their operations.
Data mapping helps you understand what PII you have, where it lives, and determine how to best secure data to meet regulations. Organizations must also implement robust measures to safeguard PII, along with a compliance policy and PII security measures, which are all critical to maintaining PII regulation compliance.
We get it. PII is complicated. Software such as Osano’s data discovery tools, PII tracking API and data mapping can help make it less stressful.
Data Mapping Checklist
Need to track down PII at your organization? Then you need data mapping. Our checklist walks you through all the basics to understand how best to map your organization's data/
Download Your Copy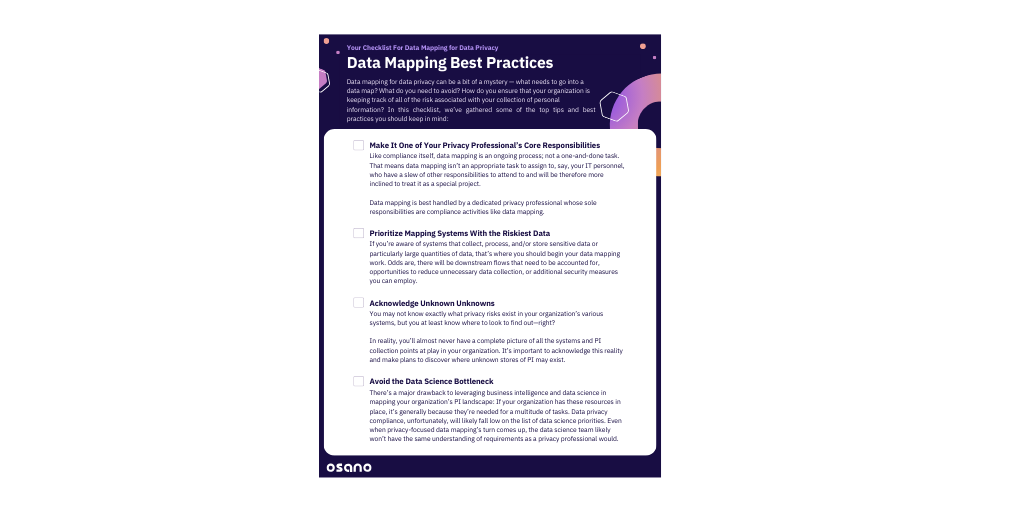
Osano Staff
Osano Staff
Osano Staff is pseudonym used by team members when authorship may not be relevant. Osanians are a diverse team of free thinkers who enjoy working as part of a distributed team with the common goal of working to make a more transparent internet.
.webp?width=1220&height=1090&name=Osano-guarantee-seal%20(1).webp)